
Comparing trade data providers-APP, download it now, new users will receive a novice gift pack.
International procurement intelligence
author: 2024-12-24 03:08HS code alignment with sustainability targets
author: 2024-12-24 03:02HS code-based freight consolidation
author: 2024-12-24 02:56Import data trends visualization
author: 2024-12-24 02:01HS code-driven trade finance optimization
author: 2024-12-24 01:30Insightful trade route analysis
author: 2024-12-24 03:14HS code-driven tariff reduction strategies
author: 2024-12-24 02:06Cost-effective trade analytics solutions
author: 2024-12-24 01:12Special economic zones HS code strategies
author: 2024-12-24 01:08Industrial lubricants HS code classification
author: 2024-12-24 01:00 How to integrate trade data with RPA
How to integrate trade data with RPA
891.52MB
Check Automated trade documentation routing
Automated trade documentation routing
558.12MB
Check Real-time shipment inspection data
Real-time shipment inspection data
976.73MB
Check How to ensure transparency in supply chains
How to ensure transparency in supply chains
337.73MB
Check How to evaluate free trade agreements
How to evaluate free trade agreements
374.26MB
Check Data-driven trade invoice verification
Data-driven trade invoice verification
882.32MB
Check Dairy sector HS code forecasting
Dairy sector HS code forecasting
668.87MB
Check How to comply with export quotas
How to comply with export quotas
221.91MB
Check Global trade metadata enrichment
Global trade metadata enrichment
274.36MB
Check Trade data-driven transport mode selection
Trade data-driven transport mode selection
461.67MB
Check Pharmaceutical HS code compliance in India
Pharmaceutical HS code compliance in India
944.22MB
Check Trade intelligence for aerospace industry
Trade intelligence for aerospace industry
894.41MB
Check How to map trade data to SKUs
How to map trade data to SKUs
859.95MB
Check Customized HS code dashboards
Customized HS code dashboards
127.48MB
Check How to interpret global trade indices
How to interpret global trade indices
511.28MB
Check How to comply with export quotas
How to comply with export quotas
424.39MB
Check HS code advisory for inbound compliance
HS code advisory for inbound compliance
245.46MB
Check Biodegradable materials HS code verification
Biodegradable materials HS code verification
888.96MB
Check HS code-driven cost-benefit analyses
HS code-driven cost-benefit analyses
153.18MB
Check How to align sourcing strategy with trade data
How to align sourcing strategy with trade data
656.28MB
Check Real-time import quota alerts
Real-time import quota alerts
655.76MB
Check international trade research
international trade research
634.42MB
Check Data-driven supply chain partnerships
Data-driven supply chain partnerships
596.15MB
Check Real-time supply chain event updates
Real-time supply chain event updates
891.36MB
Check Gourmet foods HS code classification
Gourmet foods HS code classification
355.48MB
Check How to find emerging export markets
How to find emerging export markets
751.78MB
Check Cocoa and chocolate HS code insights
Cocoa and chocolate HS code insights
145.48MB
Check Customs duty optimization strategies
Customs duty optimization strategies
276.21MB
Check Trade data solutions for wholesalers
Trade data solutions for wholesalers
959.19MB
Check Real-time import export alerts
Real-time import export alerts
334.52MB
Check How to track global shipments
How to track global shipments
922.64MB
Check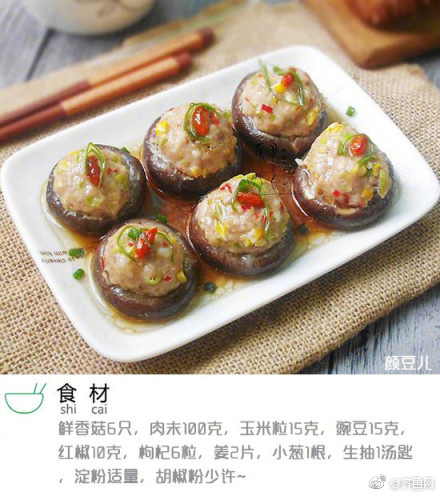 HS code-based FTA utilization
HS code-based FTA utilization
129.62MB
Check How to identify correct HS codes
How to identify correct HS codes
663.12MB
Check Trade Data intelligence
Trade Data intelligence
398.21MB
Check HS code-based customs dispute resolution
HS code-based customs dispute resolution
756.11MB
Check Trade data-driven portfolio management
Trade data-driven portfolio management
698.34MB
Check
Scan to install
Comparing trade data providers to discover more
Netizen comments More
2785 Global trade data normalization
2024-12-24 02:48 recommend
2572 Australia HS code tariff insights
2024-12-24 01:38 recommend
2105 Global trade compliance dashboards
2024-12-24 01:24 recommend
2207 Global trade finance benchmarking
2024-12-24 01:16 recommend
1687 Real-time supplier performance scoring
2024-12-24 00:59 recommend